The zero trust framework is the next step in the evolution of each company’s security strategy. Let’s look at the details of the zero trust paradigm and how companies may successfully implement their version of ZTA by putting the best practices into practice.
Research firm Garter recently forecasted the future of the zero trust architecture in its recent status report , Zero Trust Architecture and Solutions. The report said that in place of virtual private networks, about 60% of enterprises will utilize a zero trust security architecture by 2023. This is because many workers now work remotely, and business networks are growing more sophisticated. Hackers have more opportunities to access a company network and steal information. Cybersecurity experts have developed the zero trust method to shield organizations from today’s risks. Let’s examine its operation in more detail.
What is zero trust?
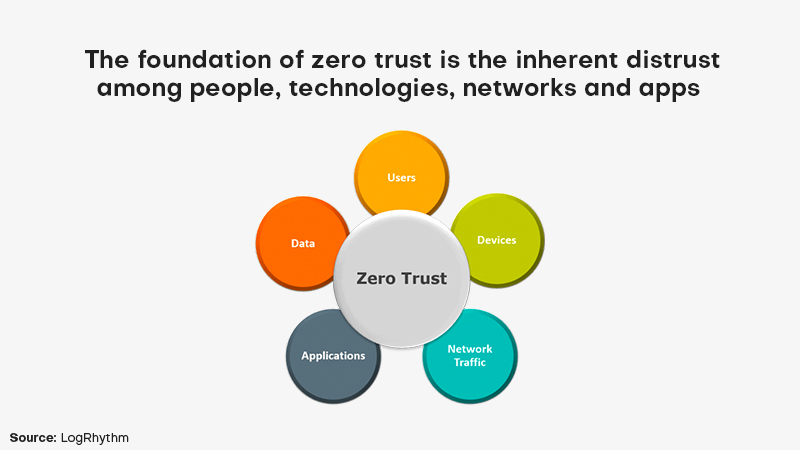
“Zero trust is a way of thinking, and not a specific technology or architecture,” says Gartner Distinguished VP Analyst Neil MacDonald. “It’s really about zero implicit trust, as that’s what we want to get rid of.” When network security was initially established, individuals built a perimeter where everyone had mutual trust and shared access to resources. Contrarily, the idea of zero trust is built on mistrusting everyone and everything, whether they are inside or outside the network boundary.
Why should enterprises utilize zero trust?
Instead of cordoning off IT operations behind a secure network fence, zero trust takes a different approach to security. The emergence of remote working methods, the growth of endpoints and BYODs, diverse and networked technologies across clouds and business data centers, as well as sheer complexity have all contributed to its increased adoption. Rather than attempting to safeguard outer walls, zero trust works to limit the potential harm by assuming that such security measures will collapse or have already been breached.
Companies must adopt a tighter position on enhancing data protection and systems as technology advances, security standards are formed, and privacy legislation is put into place, particularly if business norms for people operating remotely alter as a result of the outbreak. The problems listed below are examples of those for which zero trust can be a suitable approach:
- Network perimeter security in a dynamic environment: Particularly when systems are dispersed over cloud environments and on-premises, ZTN enables enterprises to retain the security of continuous changes in the network infrastructure.
- Transition to the cloud: Another difficulty is switching to cloud infrastructure since new data exchange methods have emerged, if occasionally unreliable. The traffic sometimes prohibits remote work that IT experts frequently block.
- Accountability issues with users: ZTN uses precise user access restrictions and an “authenticate first” strategy to implement access responsibility and related user behaviors.
- Excessive security programs: Most firms do not have the funding to cover the excessive number of security solutions needed to protect the enterprise infrastructure.
Best Practices for Implementing Zero Trust Correctly
Remember the three principles
Zero Trust is a comprehensive, end-to-end security approach built on three key tenets:
- Never trust anything without first checking it: Always authenticate and approve using all the information at your disposal, such as user identification, location, equipment, information sources, service, and workload. Constant verification implies that no people, devices, or domains are trusted. On the other hand, zero trust views everything and everyone as a possible threat.
- Assume breach: If you approach prospective threats with the assumption that your systems have already been breached, you may strengthen your overall security and lessen the effect if an intrusion does happen. Restrict the “blast radius,” or the range of possible harm caused by a breach, by controlling access, decreasing your attack surface, confirming end-to-end encryption, and closely watching your network.
- Zero trust adheres to the Principle of Least Privilege (PoLP), which is the practice of limiting access rights for everyone and granting just the minimal powers necessary to fulfill its task. To put it another way, PoLP restricts network-wide access to individuals, groups, apps, etc., which might make your network less secure, thereby expanding the attack surface in the case of a breach.
Use multi-factor authentication (MFA) to confirm the user at all times
The day when using a password to securely confirm a user’s identity was commonplace is long past. User names and passwords are now vulnerable to phishing attacks, malware scanning, and dark web purchases. Credentials must thus be strengthened via MFA, which relies on something you are, something you know, or something you have.
No matter who is accessing the resource—an application or infrastructure—multi-factor authentication must be used, whether they are end users, privileged users, partners, customers, or outsourced IT. Organizations should impose more stringent authentication requirements on users who want to enhance their privileges or access the most sensitive data.
Always check the device
Devices need to be verified before they can be trusted, just like users. Identity-centric endpoint controls must be included in order to achieve zero trust security. This implies that any device used to access corporate resources must first enroll in order for it to be identified and confirmed.
The best part is that device enrollment procedures aren’t as difficult as they were. The self-service enrollment method has a little to nonexistent administrative burden. Look for an automatic certificate enrollment that protects access to Exchange, VPN, and Wi-Fi, supports all widely used mobile devices and ensures that only designated users have access to information.
Continue to keep an eye on the traffic
All resources may be better safeguarded by funneling all logs to one area and keeping an eye on them for malicious behavior. Deep packet inspection tools and other network security monitoring technology can be used for this. Additionally, unwelcome traffic may be successfully monitored and blocked by using automation and orchestration. Since achieving zero trust is a continuous effort, it is important to regularly review all logs and make changes to increase visibility into all resources.
Establish a robust device identity
The foundation of a zero trust architecture is device identity. It serves as the foundation for procedures such as permission, authentication, and others. It must be powerful and distinctive.
The device identity must be connected to the device rather than the user. Even if a device is hidden behind a NAT or is not connected to a network, it should still be feasible to identify it, along with:
- Verified by the network: It should not be possible for a device to claim more than one identity or an identity that does not belong to it.
- Even if the gadget is modified or replaced, it must remain persistent and unaltered.
- Time-tested and verifiable: It ought to be easy to determine if a device is still operational or has been deactivated.
- Cross-network verifiability: The same device needs to be able to authenticate itself while joining other networks, even open ones.
Adopt zero trust policies
One of the most important and time-consuming aspects of establishing a powerful ZTN is working to build regulations. In order to accept or deny suitable traffic flow, businesses must really grasp their protection surface. All network workloads should have these granular controls applied using security technologies.
The best way to create and execute zero trust policies is to come up with responses to the following questions: Who utilize the services? They need access to what, exactly? When will they need access? Where are the endpoints and individuals that are seeking access positioned? Why is data access being requested? Finally, how does the organization authorize or permit access?

